Published:
June 1, 2021, 01:06 GMT
Specialist Zach Duffman has warned of the danger of the Lightning O.MG, a replica of the original Apple cable developed by inventor Mike Grover and released in 2019, that has the ability to geolocate and record keystrokes, among other functions.
Cybersecurity expert Zach Duffman explained In an article published last Saturday in Forbes, Why should you? Stop using other people’s iPhone or iPad cables.
The specialist warned of the dangerousness of the Lightning O.MG, an exact replica of the original cable from an Apple Developed by inventor Mike Grover and released in 2019, it features a separate Wi-Fi access point, payload storage, and geolocation and tracking capabilities. Record keystrokes, Among other jobs. These cables can be controlled by a browser: An attacker can directly enter a cable access point or connect the cable to a network to find his own way to any device.
As Grover explained in an interview with Forbes, his device was not designed to attack iPhones, but Macs and other computers that they connect to for charging or syncing. Initially, the cables were built by hand by the inventor and it was very easy to distinguish the original cables. “At the time, I just wanted to see if I could do it - produce something small enough,” he said, adding that he is not planning to equip hackers with his hardware, but instead This is what is intended as a warning.
But later the design was improved and the cables became completely exact copies. Currently - after replacing the original USB-A with a USB-C update - the iPad Pro and various models of Android “smartphones” are also at risk.
Additionally, experts have indicated that cargo storage opens up a possibility Direct attacks by “malware”- Cables can self-arm when on target and self-destroy when their location changes. They explained that there is an attack cycle that allows the user to pick up the stresses and then introduce their own stresses. This makes it possible for the device to collect information when the user is using it, and attack it when it is not.
However, Grover stressed that his cable is not actually that dangerous, because it intentionally prevented his devices in “mobile attack mode” from charging or syncing phones, ” They have a limited ability to use it without knowing the targetIt is designed for illustration and training only, he noted.
As well as that, Specialists They advise not to connect the unlocked “smartphone” to any USB port and if it is necessary to recharge the device in a public place, it is best to use its charger. They added, “USB cables are designed for data, remember.”
If you find it interesting, share it with your friends!

“Proud web fanatic. Subtly charming twitter geek. Reader. Internet trailblazer. Music buff.”



More Stories
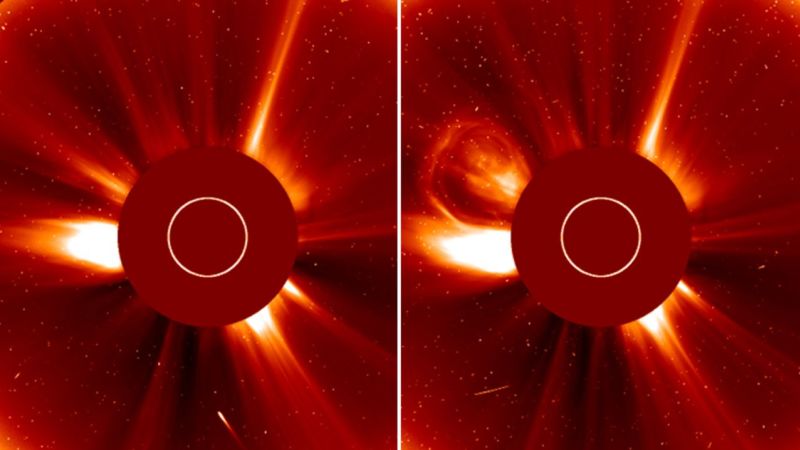
The final moments of the “Halloween Comet” were captured by the SOHO spacecraft
University of Michigan scientists have discovered what’s inside a black hole
NASA shares the scariest images of the sun in the lead-up to Halloween